Cloud computing. Internet technology. Online services. Data, information security. Connection. Thin line black web icon set. Outline icons collection.Vector illustration Stock Vector Image & Art - Alamy

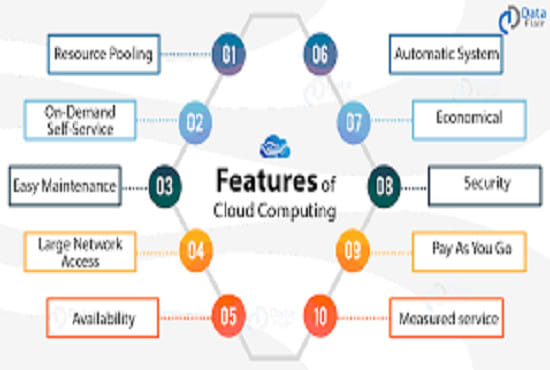
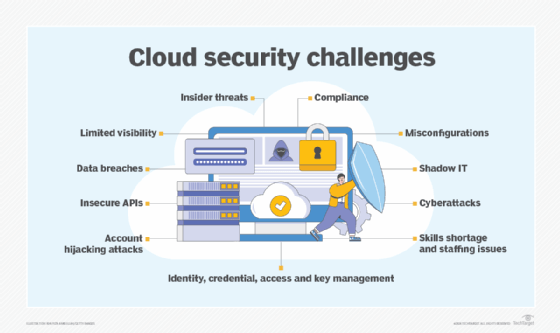
Learnuva - BCA - Ethical Hacking, Cyber Security, Cloud Computing, Data Science, Artificial Intelligence In this technological world, information technology and communication systems have become an important part of the strategic planning
Cloud Computing Icon Over The Network Connection, Cyber Security Data Protection Business Technology Privacy Concept. Stock Photo, Picture And Royalty Free Image. Image 124346671.
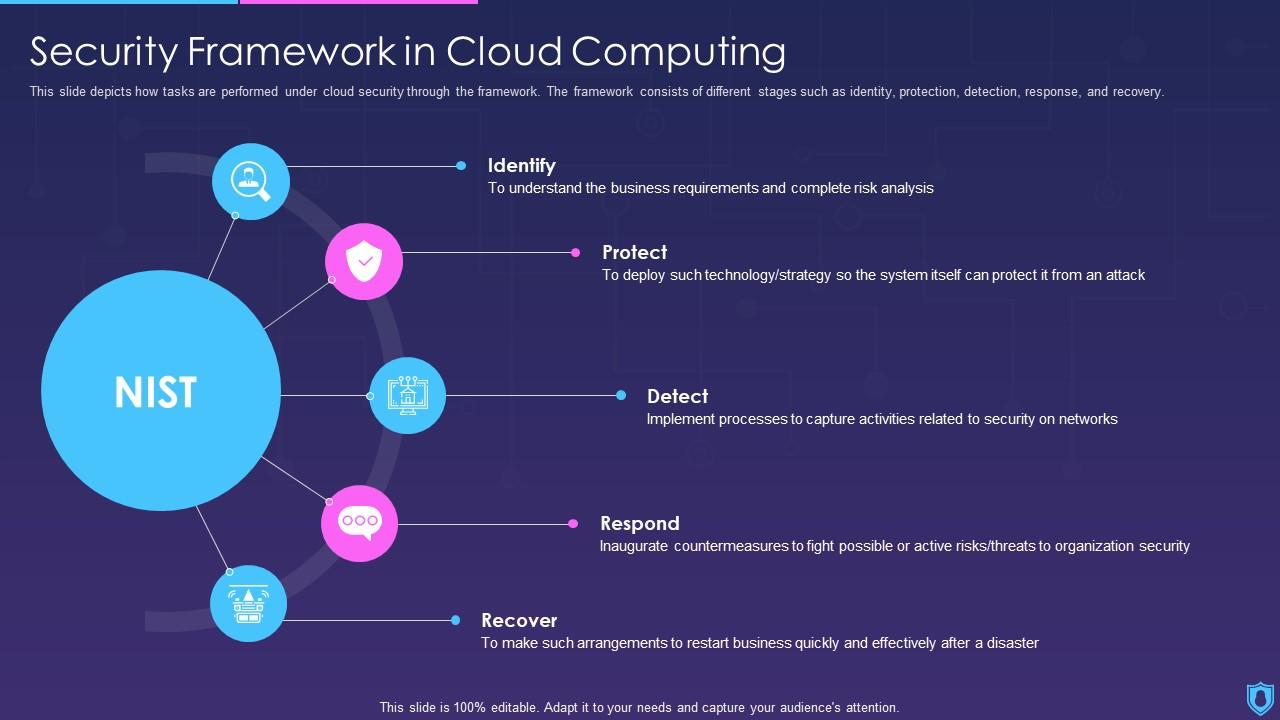
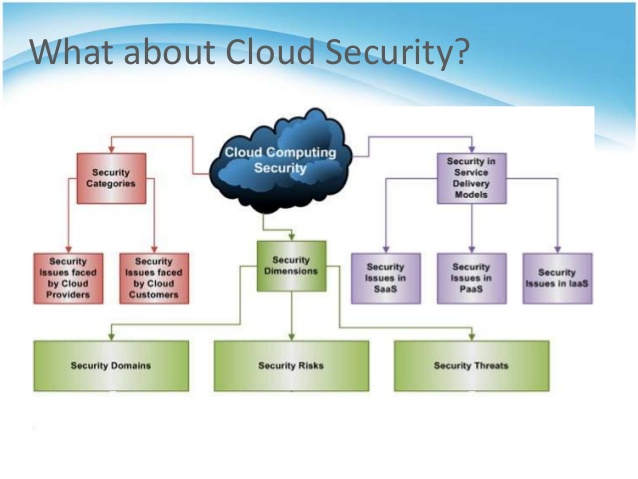
Security Framework In Cloud Computing Information Security | Presentation Graphics | Presentation PowerPoint Example | Slide Templates

Computer security Information security Data security General Data Protection Regulation Cloud computing, workflow, text, logo png | PNGEgg


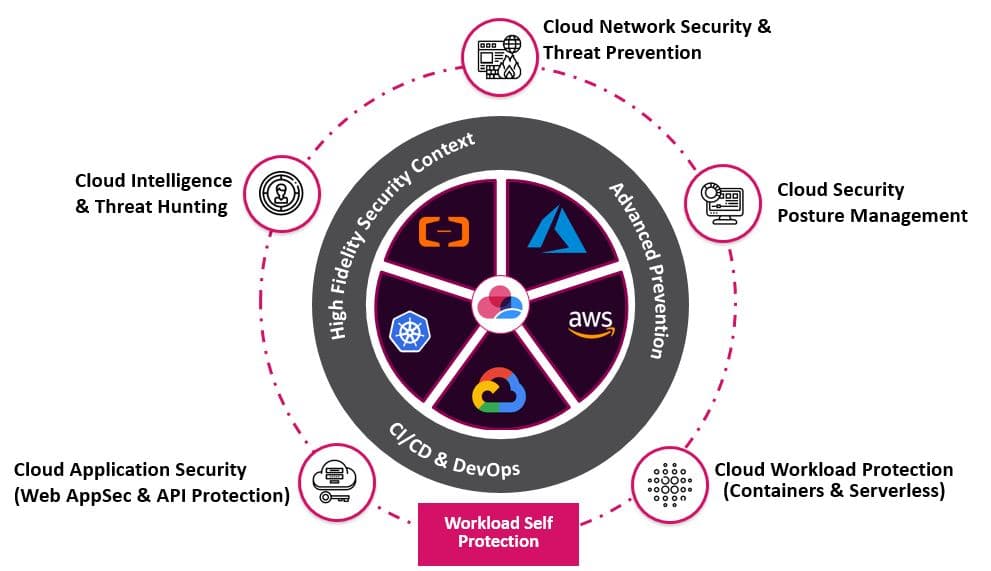
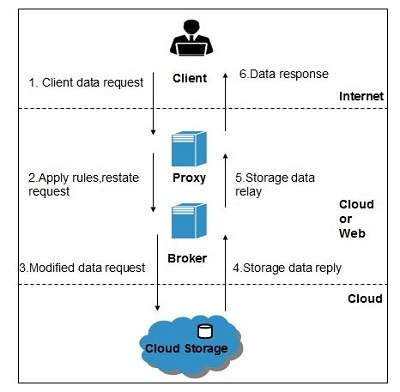




![PDF] Introducing a Security Governance Framework for Cloud Computing | Semantic Scholar PDF] Introducing a Security Governance Framework for Cloud Computing | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/3037b74aaa48564d9b1d64ae5084db628dc0aaee/5-Figure1-1.png)